ENS Certification: Why is it essential for your security?

ENS (National Security Scheme) Certification is essential to safeguard the integrity of an organization’s systems and data. In this article, we will explore why ENS certification can strengthen cyber defenses and improve partner and customer confidence.
Tabla de contenidos
ToggleGet ENS certification to protect your digital assets.
ENS Certification guarantees adequate security conditions for users. But what is the National Security Scheme? It is one of the main IT security regulations and is a strategic element in cybersecurity policies in Spain.
The first standard dates back to 2010 and was created with the aim of establishing the minimum security principles and requirements to be applied in the field of public administrations. Since then, as risks and threats have increased and become more sophisticated, it has undergone several modifications. In this way, the ENS has been evolving to improve security compliance.
The two most important modifications took place in 2015 and 2022. The fundamental change with respect to the beginning is that the ENS certification, with the different reforms, now affects all Public Administrations and Public Bodies and also those suppliers and companies that work with the Public Administrations. In other words, ENS certification is currently mandatory for the entire public sector and for suppliers that collaborate with the Administration.
ENS certification objectives
The National Security Scheme plays an important role in the digital risk management The new system provides a common framework of basic principles, requirements and security measures in order to ensure the safety and security of the data protection in the company and in the Public Administration, thus guaranteeing access, confidentiality, integrity, traceability, authenticity and data preservation, among others.

The ENS has a series of basic principles that are the guide to establish a strategy for the protection of sensitive information and thus comply with and obtain ENS certification. These basic principles are integral security and are comprised of all human, technical, material and organizational elements related to the information system. This principle is the pillar on which the implementation of the ENS is based.
The second principle is that of prevention, reaction and recovery to identify risks to the security system and prevent them from materializing or, in the event of a successful attack, to have the appropriate measures in place to stop the threat.
Also important are the sections that make it possible to establish different lines or layers of defense, the periodic re-evaluation of the measures and the identification of those responsible, who are in charge of determining compliance with the requirements and making the decisions that guarantee security.
In this sense, the Cloud & Cybersecurity by aggity proposal is specifically designed to ensure the security, integrity and operational continuity of the technological elements, as well as the processes and professionals.
Benefits of ENS certification
Obtaining ENS certification provides a number of benefits for organizations. Fundamentally, the main advantages are the availability of a system that guarantees the management of security incidents or security in corporate networks, thanks to the availability of adequate measures to protect against incidents.
In addition, ENS certification improves trust by demonstrating an organization’s commitment to information security. Certification also ensures that the company or public body complies with legal and regulatory requirements in its information security policies. ENS certification is also a requirement for participation in public procurement, which opens up business opportunities for certified organizations.

ENS certification process
The ENS is structured in three blocks that address the organizational framework, the operational framework and the protection measures. In the case of the former, regulation comprises a set of measures related to the structure of the security organization such as policies, regulations or procedures. The operational framework provides the series of processes that must be implemented within the IT system, such as risk analysis or capacity management. Finally, protection measures focus on protecting assets with very specific measures such as, for example, data encryption.
In general, in order to comply with the three blocks and obtain certification, it is necessary to carry out different actions. Among them, it is essential to perform a security analysis of the systems, processes and data; design and establish the appropriate security measures and perform an IT security audit to evaluate the effectiveness of the measures implemented and ensure compliance with the requirements of the ENS. Finally, it is only necessary to submit the application to the corresponding certification body.
Últimos posts

aggity strengthens its commitment to sustainability as a SILVER partner of “Fundación Empresa & Clima”.

aggity participates in the IBM Ecosystem Summit 2024 with an applied case of Generative AI in the food industry

Aggity, together with the multinational Fortinet, present an exclusive event in Lima on the application of Generative AI in Corporate Cybersecurity.

aggity participates in Smart Ports: Piers of the Future
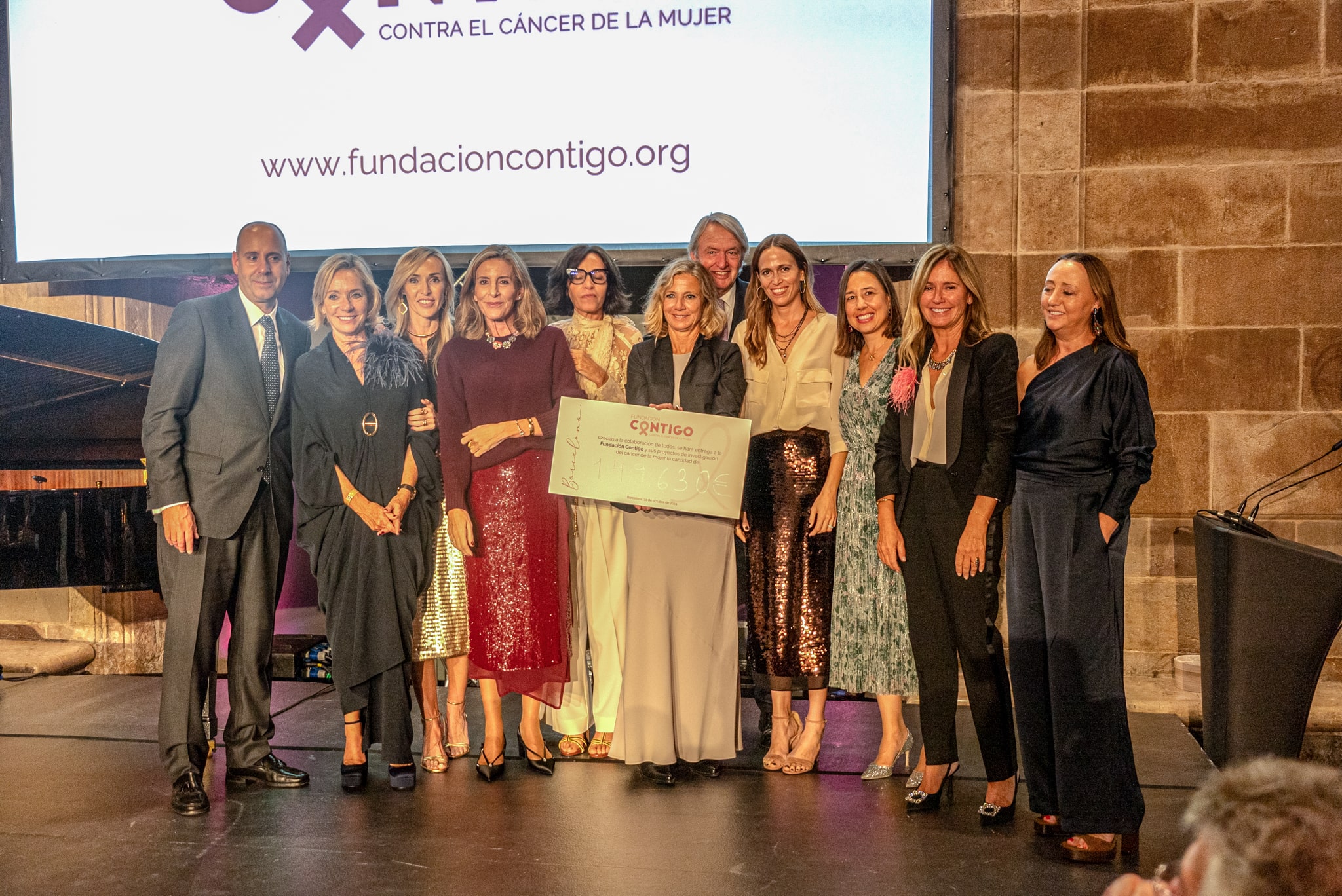
aggity Supports the Contigo Foundation at its Annual Dinner

Challenges and Opportunities of Generative AI in Industry: Our Experience at BNEW

Official Liferay Partner in Spain