How to improve cyber intelligence

Cyber intelligence is essential in a company’s security strategy as it allows to understand and mitigate digital threats in the environment. In this article, we explore proven methods and emerging strategies for strengthening cyber intelligence in an organization.
Tabla de contenidos
ToggleDiscover how to improve your cyber intelligence to better protect your business against digital threats.
Cyber intelligence is a discipline that encompasses the collection, analysis and exploitation of information in order to detect and prevent cyber attacks before they occur. It is one of the fundamental elements that make up cyber risk management and should be part of any company’s information security strategy.
Thanks to cyber intelligence, companies can stay one step ahead of malicious actors. Implementing a robust cyber intelligence system not only improves security, it also fuels cybersecurity awareness and proper preparedness that can mean the difference between a secure operation and a costly breach.
What sets cyberintelligence apart
The usual problem is that, on numerous occasions, organizations do not work correctly with cyber intelligence. For cyberintelligence to work, there are several elements to be taken into account, such as the constant monitoring of cyber security and online data sources, including social networks, public and private databases, as well as proprietary and third-party network infrastructure.
Often, cyber intelligence can be confused with other cyber intelligence tools that focus, for example, on vulnerability assessment or cyber attack prevention.
What sets cyber intelligence apart from other cyber defense techniques is that it focuses on understanding the tactics, motivations and capabilities of cybercriminals using threat intelligence sources or dark web forums. With the data obtained, companies can implement countermeasures and collaborate with other organizations to increase defenses. In contrast, traditional cyber security focuses more on protecting enterprise data and detecting known threats.

Importance in corporate security
Cyber intelligence is a key element in an organization’s cyber mitigation strategies. Cybersecurity software solutions such as those from aggity Cyber & Cloud help make cyber intelligence effective, but it is important to understand that this discipline relies on data collection and analysis to understand, mitigate threats and respond to cyber incidents.
These processes involve the use of technological tools to gather information from digital sources and extract meaningful data to enable correct decision making. Among the most common tools for extracting such data are the Web Scrapingwhich allows structured and unstructured information to be extracted from websites in an automated manner; the use of APIs for accessing data from online services such as social networks and threat analysis platforms, or the network sensorsThe software is designed to monitor network traffic in order to identify anomalous or suspicious activity in real time for subsequent analysis.
Threat analysis techniques
In addition to obtaining data to make decisions, digital threat analysis is vital to any successful cyber intelligence strategy. Cybersecurity risk analysis techniques are what will enable the cybersecurity department to understand and mitigate the risks it faces.
These techniques require a systematic process of collection, evaluation and action based on relevant data to effectively identify and respond to threats. Among the most common procedures is vulnerability scanning, which involves the assessment of systems, applications and networks to identify potential weaknesses that could be exploited by malicious actors.
It is also common in cyber attack prevention to systematically perform malware analysis to understand the behavior and impact of malicious programs such as viruses, Trojans and ransomware.
The techniques used also include threat intelligence analysis, in which they collect and evaluate data to identify patterns and trends in the threat landscape and anticipate potential attacks. Equally important is the analysis of anomalous behavior to identify unusual or suspicious activity on systems and networks that could indicate a security compromise.

Challenges and limitations
Like any other discipline in the world of cybersecurity, cyber intelligence also faces a number of challenges. The main challenge is the constant evolution and increase in cyber threats, but compliance with security regulations and cybersecurity training are also important.
Regarding the former, it should be stressed that companies are obliged to comply with regulations such as the General Data Protection Regulation (GDPR), to protect data privacy and avoid legal and financial penalties.
In addition, because cybersecurity is such a fast-changing environment, it is essential that employees receive training in cybersecurity. continuous cybersecurity training to keep up to date with the latest attack trends and techniquesespecially when the current situation is characterized by a shortage of qualified professionals, making it difficult to recruit and retain talent.
Últimos posts

aggity strengthens its commitment to sustainability as a SILVER partner of “Fundación Empresa & Clima”.

aggity participates in the IBM Ecosystem Summit 2024 with an applied case of Generative AI in the food industry

Aggity, together with the multinational Fortinet, present an exclusive event in Lima on the application of Generative AI in Corporate Cybersecurity.

aggity participates in Smart Ports: Piers of the Future
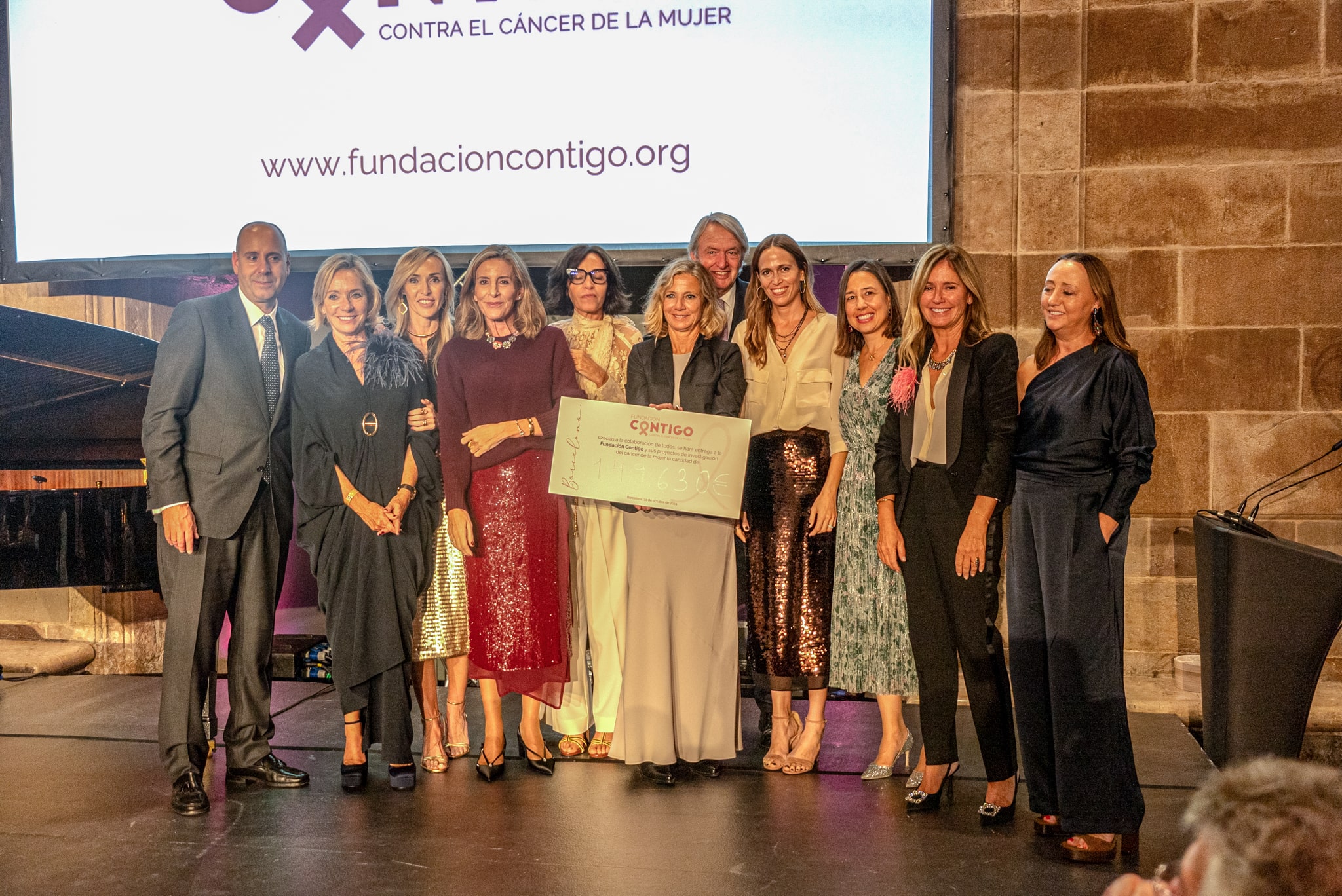
aggity Supports the Contigo Foundation at its Annual Dinner

Challenges and Opportunities of Generative AI in Industry: Our Experience at BNEW

Official Liferay Partner in Spain