Web Security Audit: Protect your Company with Aggity

Through detailed analysis, aggity evaluates the robustness of systems and applications, identifying potential vulnerabilities and weaknesses. aggity’s team of cybersecurity experts provides organizations with customized recommendations to strengthen their defenses and safeguard the integrity of your information and assets.
Tabla de contenidos
ToggleFind out how to protect your company with our web security audit.
When establishing and implementing any type of cybersecurity strategy, it is necessary to have the right partner to guide, orient and help the organization to implement the appropriate cybersecurity measures, as well as to detect the company’s vulnerabilities.
aggity is the perfect partner that guarantees the company the peace of mind of having a solid protection against cyber-attacks and ensures the continuity of operations. In this context, aggity’ s web security audit is a comprehensive solution for assessing and improving the protection of companies against any type of cyber threat.
What is a web security audit
Before listing the advantages provided by aggity’s solution, it is necessary to explain what an aggity solution consists of. web security auditThis is an essential process in any process cybersecurity strategy and aims to assess and analyze the security of a website by identifying vulnerabilities that can be exploited by cybercriminals.
This practice is essential to ensure data protection, online security, perform a cyber risk assessment cyber risk assessment or discover if there is any deficit in security compliance, among others.
The importance of performing a web security audit by an expert partner such as aggity is vital for any organization because during a web security audit a comprehensive review of the technological infrastructure underlying the website, including its code, server configurations, databases and other relevant layers. aggity’s audit proposal proposes different actions:
Review server security settings
This process verifies that the server has a secure configuration, which includes a security scan including firewalls, access restrictions and appropriate SSL/TLS configurations.

Update software and plugins
By doing so, aggity’s experts ensure that all software used on the organization’s website, including the CMS and plugins, is updated to the latest versions with security patches.
The updates are intended to address security vulnerabilities, improve stability and add new features to prevent the web from being exposed to cyber-attacks. In addition, a vulnerability scan is also performed to identify possible weaknesses and security holes in the site.
Protection against brute force attacks
One of the most common web vulnerabilities is usually related to the access forms and passwords used. In this case cybercriminals try to crack passwords by trying multiple combinations, so to mitigate these attacks it is important to implement measures such as temporary blocks on the website after several failed attempts and to use robust password policies.
It is also important to establish security measures for forms and sensitive data. The web security audit provided by aggity reviews the security of forms that collect sensitive data and ensures that data is transmitted and stored securely. In this sense, aggity’s experts also guarantee network security by preventing malware from circulating through them.
Authentication and authorization tests
This is another element of aggity’s web security audit. Authentication and authorization testing is an essential part of IT security as it allows to verify that the authentication and authorization of users on the website are working correctly and that only authorized users have access to certain functions or areas.

Penetration testing
In systems auditing , penetration penetration testing are becoming increasingly important in system auditing. Also known as pentesting, these are controlled computer security assessments that simulate real cyber attacks to identify vulnerabilities in systems, networks or applications and assess cyber risks. The goal is to reveal potential weaknesses before cybercriminals can exploit them.
These are just some of the actions performed in aggity’s web security audit. However, the proposal Cloud & Cybersecurity by aggity also includes code security validation, session management, content security policies, code injection protection, database access security, resource access control, backup and recovery, as well as continuous monitoring.
Últimos posts

aggity strengthens its commitment to sustainability as a SILVER partner of “Fundación Empresa & Clima”.

aggity participates in the IBM Ecosystem Summit 2024 with an applied case of Generative AI in the food industry

Aggity, together with the multinational Fortinet, present an exclusive event in Lima on the application of Generative AI in Corporate Cybersecurity.

aggity participates in Smart Ports: Piers of the Future
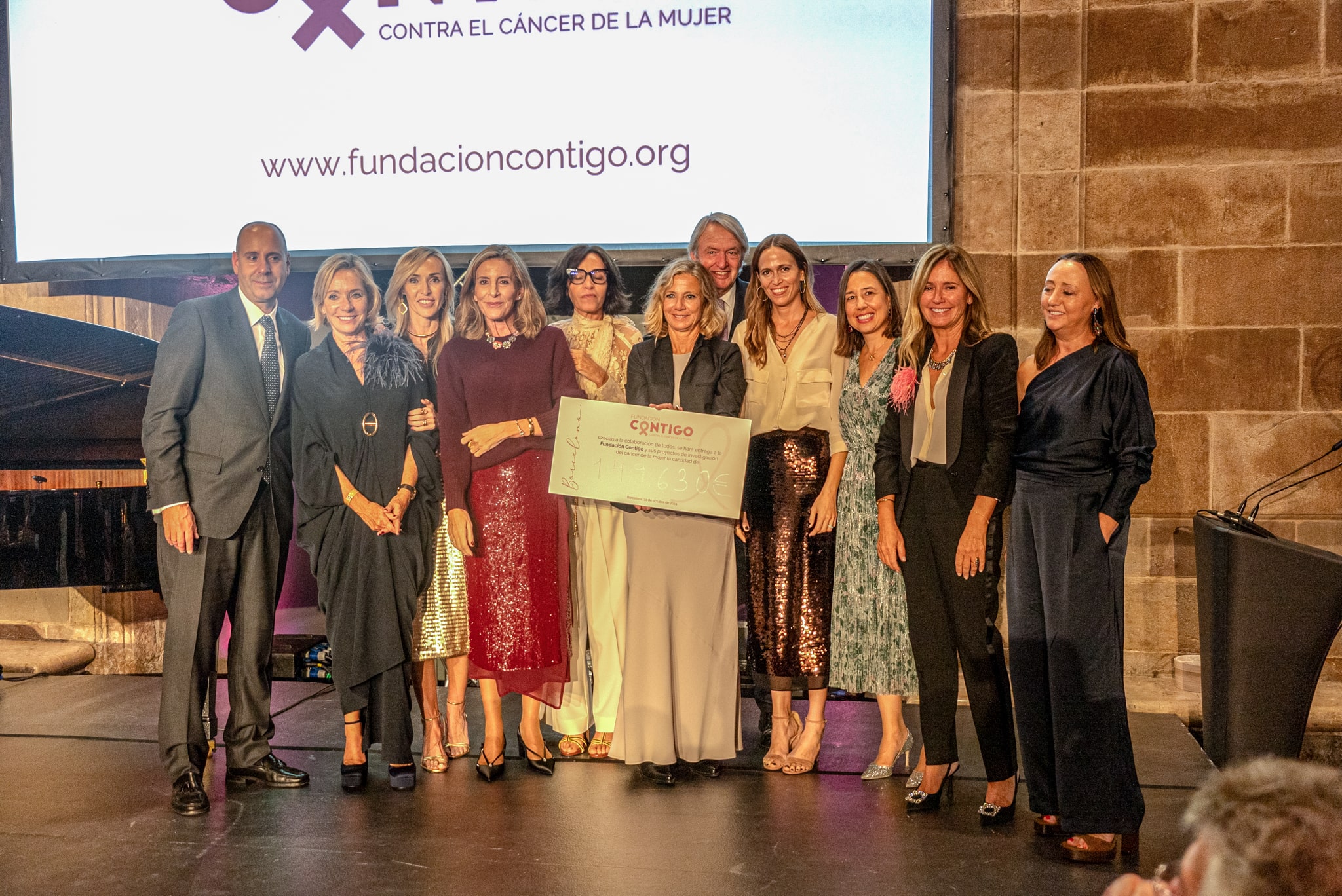
aggity Supports the Contigo Foundation at its Annual Dinner

Challenges and Opportunities of Generative AI in Industry: Our Experience at BNEW

Official Liferay Partner in Spain